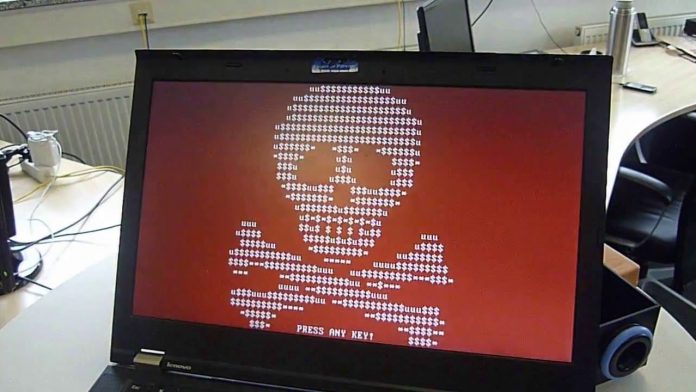
According to the latest alert by the U.S. Federal Bureau of Investigation (FBI), an upsurge in dual ransomware attacks is causing additional concerns in the cybersecurity world. The warnings indicate that multiple ransomware assailants are targeting the same victims twice, with the operations executed close to each other. This new trend presents intensified risks to entities that have already undergone digital breaches.
A Spectrum of Ransomware Families Involved
Based on FBI's observations, multiple ransomware families are employed by attackers within the victims' network. Notable ransomware variants discovered include AvosLocker, Diamond, Hive, Karakurt, LockBit, Quantum, and Royal. Consequently, the dual ransomware assaults have resulted in a combination of data breaches, heightened network compromises, and increased financial losses due to enforced ransom payments.
Simultaneously, the FBI noticed that several ransomware groups are escalating the use of unique data theft, wiper tools, and malware to exert further pressure on their victims, compelling them to negotiate. They have modified known data theft tools with their specific code to elude detection, while dormant data wipers were deployed until a specific time to avoid detection or used intermittently to corrupt data.
Cyber Defense Strategies Urged
Despite the mounting occurrence of dual ransomware attacks, this development is not entirely new. In the past, systems victimized by cyber threats have recorded infections caused by more than one strain of ransomware. An instance of this was observed in an incident handled by Symantec's Threat Hunter Team where a LockBit ransomware deployment failure led to the discovery of a new ransomware family named 3AM.
In response to these recent threats, the FBI's alert provides crucial recommendations for network defenders. These include preparation for rapid response to potential cyber incidents, enhancement of identity and access management, implementation of preventative controls, and a revamped approach to vulnerability and configuration management. These steps are crucial in mitigating the increased risk posed by dual ransomware attacks.
Recent Ransomware Warnings
Last month, Cybersecurity platform Securonix has recently highlighted a surge in cyberattacks aimed at Microsoft SQL (MSSQL) servers. This attack campaign is designed to exploit vulnerabilities in these servers to deploy the FreeWorld ransomware. Threat actors are scouting for Microsoft SQL servers burdened by weak or default credentials. Once they sport a target, these actors deploy their attack method to gain access and introduce the FreeWorld ransomware payload.
Last week, Sony was reportedly breached in an attack by a new ransomware group. The tech giant is currently investigating allegations of a significant data breach following claims made by a group identifying themselves as RansomedVC. This group has asserted responsibility for the alleged hack, stating that they have compromised all of Sony's systems.