When a security researcher discovered a flaw related to Apple software recently, there was concern an exploit would allow attackers to remote access and change the “Sign in with Apple” feature. After learning of the issue, Apple responded and has fixed the critical flaw.
According to researcher Bhavuk Jain, the vulnerability would allow bad actors to take control of third-party application accounts remotely.
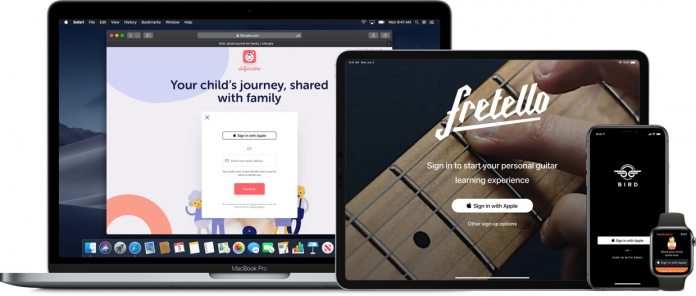
Sign in with Apple was introduced by the company at its WWDC developer conference in 2019. Cupertino promotes the feature as a way to easily and securely sign into third-party apps and websites. It leverages the company's backend authentication system and replaces logins such as for Facebook and other third-party services.
Jain discovered the problem when participating in a bounty program. Apple honored the program and paid the researcher $100,000 for this discovery. After, the company developed a fix that has since been rolled out.
“In the month of April, I found a zero-day in Sign in with Apple that affected third-party applications which were using it and didn't implement their own additional security measures,” said Jain, in a blog post. “This bug could have resulted in a full account takeover of user accounts on that third-party application irrespective of a victim having a valid Apple ID or not.”
Potential Exploit
It seems the sign in tool would not validate a user properly. It would use their Apple email address as client-side verification. However, any requests from the sign in with Apple feature were not checked to see if they came from the user. Hackers would be able to use a victim's Apple ID email address and trick Apple into believing it came from the legitimate account holder.
Once the attacker had bypassed Sign in with Apple, they could access third-party apps, including social media.
“I found I could request JWTs for any Email ID from Apple and when the signature of these tokens was verified using Apple's public key, they showed as valid,” Jain says. “This means an attacker could forge a JWT by linking any Email ID to it and gaining access to the victim's account.”
Jain points out Cupertino's investigation found there were no active exploits due to the vulnerability.