The administrative capacity of Azure Active Directory (AD) with the announcement of three new administrative roles. In a blog announcing the additions, Microsoft says the roles will help enterprise customers access advanced security features without having to use highly-privileged global administrators.
Customers have frequently asked for more access to the risks impacting their data and users, Microsoft says that three new roles make it easier for Azure AD users to make Azure AD Identity and Azure AD Privileged Identity Management (PIM) more visible and easier to manage.
“These three new roles “Privileged Role Administrator”, “Security Administrator” and “Security Reader” simplify managing and accessing reports in Azure Active Directory Identity Protection and Azure AD Privileged Identity Management (PIM). Using these new roles, organizations can take advantage of these new security capabilities without having to add additional highly-privileged global administrators.”

Access to Azure AD Identity Protection previously required a global administrator privilege, but with the new Security Reader role allows a user to view reports and settings in Azure Active Directory Identity Protection. Security Administrator can view reports and manage settings in Azure AD Identity Protection.
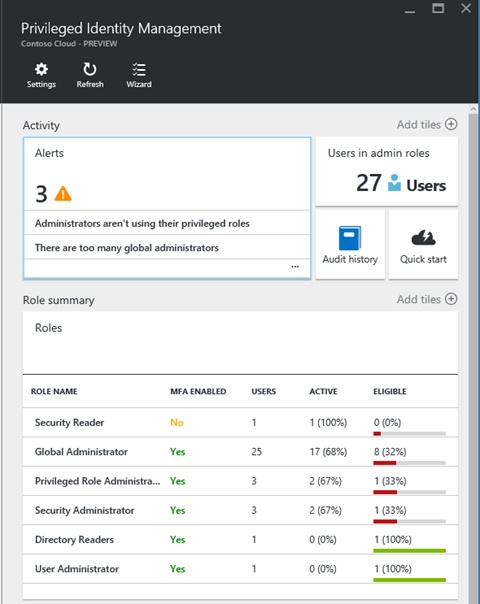
Azure Active Directory Privileged Identity Management still needs global admin access when viewed in a directory. The service is still in preview and Microsoft says the new roles give admins the ability to manage role assignments and view the audit history. Security Administrator and Security Reader roles allow access to assignments and settings.
Microsoft adds that assigning a user to one of the roles is easy:
“The best way to add someone to the Privileged Role Administrator, Security Administrator, or Security Reader roles is through Azure AD PIM. Select the role, click Add, select a user, and click OK. That user will be made eligible to activate the role. The user can then activate the role for a predefined time period, when they need to use Azure Active Directory Identity Protection or Azure AD PIM.”
The company goes into detail on what each role allows in its blog post, which is worth checking out.






