Security researchers from ESET have uncovered an expansion of the Stantinko botnet that's using YouTube videos to share proxy IPs. The botnet now consists of 500,000 PCs and has moved from spreading adware and password-stealing to crypto mining.
The currency in question is Monero, with most infected PCs in Russia, Ukraine, Belarus, and Kazakhstan. However, while the mining methods used are quite popular – a modified version of xmr-stak, its methods to hide its activities are note-worthy.
The creators of Stantinko has heavily modified xmr-stak, removing some functionality and strings to avoid detection. On top of that, it doesn't directly communicate with its mining pool. Instead, it uses proxies whose IP addresses are shared via YouTube videos.
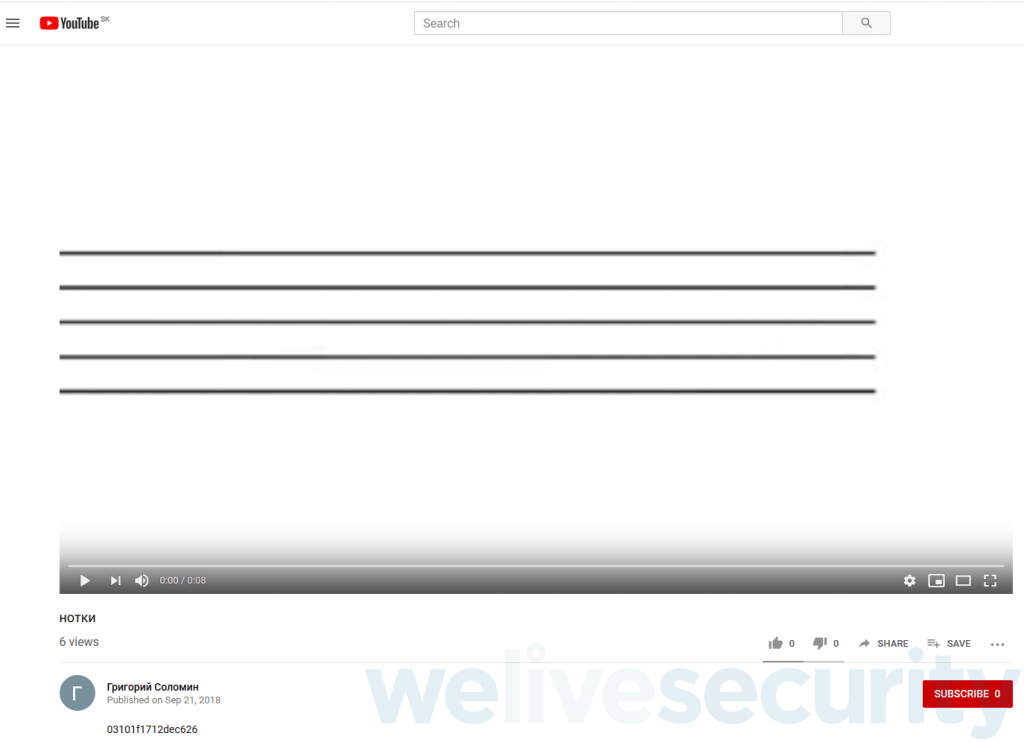
Hexidecimal and Exclamation Marks
Videos with Russian language titles contain a description with hexadecimal which corresponds to two IP addresses. The addresses are further enclosed by exclamation points to make parsing easier and protect against changes to the video's HTML structure.
“Currently the module receives a video identifier as a command line parameter instead. This parameter is then used to construct the YouTube URL, in the form https://www.youtube.com/watch?v=%PARAM%,” explains ESET. “The cryptomining module is executed either by Stantinko's BEDS component, or by rundll32.exe via a batch file that we have not captured, with the module loaded from a local file system location of the form %TEMP%\%RANDOM%\%RANDOM_GUID%.dll.”
After being informed of the methods, YouTube removed all of the offending videos. This should prevent some of the stealth of the script, as PCs are less likely to flag malware accessing a trusted site like YouTube.
Stantinko has now been around since 2012 and this recent evolution shows that it's not going to disappear any time soon. All consumers can do is monitor their PC for suspicious resource usage, avoid suspicious links, and keep their security software updated.