Microsoft has been making some great improvements to the Azure IoT Hub over the year, and many of them have focused on security. Last month, it opened its Security Program, which gives customers access to certified auditors that can ensure the safety of cloud devices.
However, that's not the end to this years' security improvements. Azure IoT now supports IP filtering. This feature lets admins set up policies that dictate what devices can connect to their network.
Supported IP Filtering Methods in Azure IoT Hub
At first glance, Azure IoT's IP filtering looks very robust. You can choose to accept only certain IP addresses, block specific ones, or both at the same time. There are also plenty of protocols supported, as listed below:
- MQTT
- AMQP/WS
- MQTT/WS
- HTTP/1
Importantly, rejected IPv4 addresses aren't told about any rules in place. Instead, they receive an unauthorized 401 code. This ensures that the individual policies remain opaque and are less likely to be worked around. The filter is limited to a maximum of ten rules for each individual IP address or subnet using CIDR-notation.
It's important to note that Azure IoT Hub can already limit connections via Express Route. However, according to Microsoft, “IP filtering enables an additional level of security by enabling administrators to only accept Express Route connections.”
Ease of Use
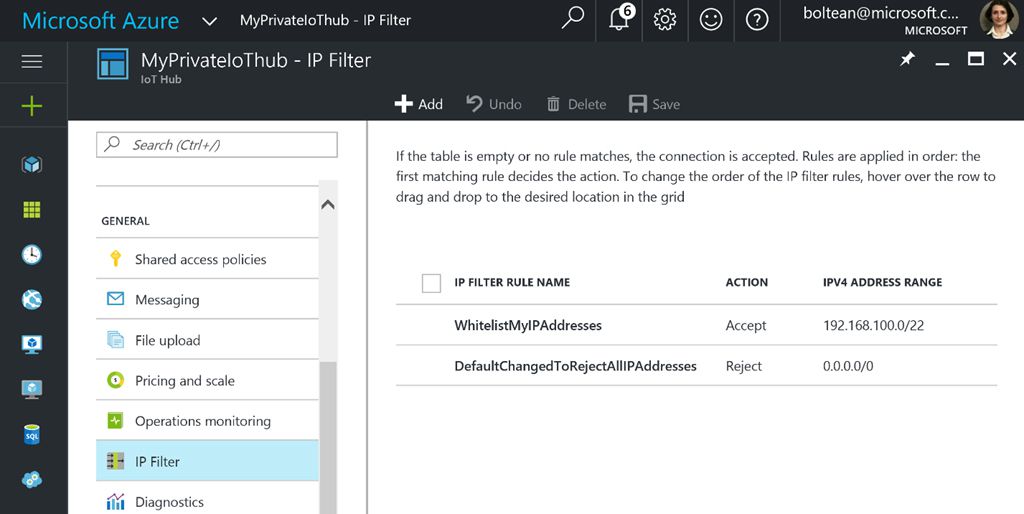
Azure IoT IP filtering also has the advantage of a very simple interface. To reject an IP, you simply navigate to the IP Filter pane, hit add, and enter the name, IPv4 address, and action.
This can also be used to allow specific connections, as well as create a range of addresses that can connect. To make full use of this functionality, you have to create two rules. The first simply blacklists all addresses, while the second overrides it with an accepted range.
It's all fairly intuitive, and Microsoft has plenty of guidance if users get stuck. You can find further details on how to implement IP filtering on the Azure blog.






