Microsoft has announced a new feature called Collaboration Security for Microsoft Teams, which is now available for public preview. The feature is designed to protect organizations against cyber-attacks that specifically target collaboration platforms like Teams.
Collaboration Security for Microsoft Teams brings the full feature set of Microsoft Defender for Office 365 as a so-called Extended Detection and Response (XDR) solution to Microsoft Teams. Using it, users benefit from the same level of protection that they have for their email environments across prevention, detection, and response for their Teams messages, files, and links.
Report-Feature for Suspicious Messages
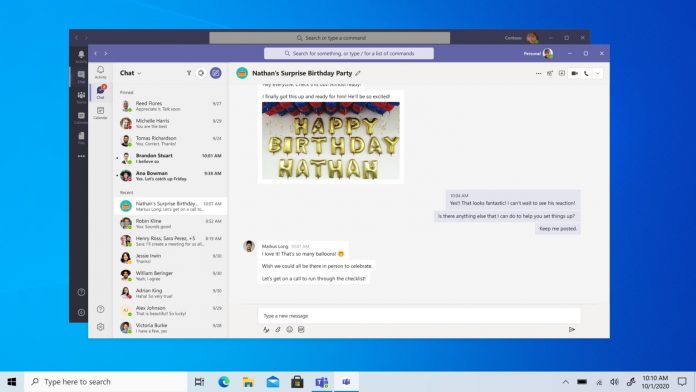
In addition to providing a high level of protection, Collaboration Security for Microsoft Teams introduces new capabilities to help build cybersecurity awareness and resilience for end-users. For example, end-users can report suspicious messages directly in Teams by clicking on a new “Report message” option in the message menu. This triggers an alert to the security team, who can view the reported message in the Microsoft 365 Defender portal for further investigation. Furthermore, the feature also allows for automatic removal of malicious messages and simulation and training resources for potential attacks.
Collaboration Security for Microsoft Teams integrates with Microsoft 365 Defender, a unified security operations (SecOps) experience that correlates all signals and alerts across other domains, including endpoints, identities, email, DLP, and SaaS apps. The integration gives users a comprehensive and holistic view of their security posture and responds to threats faster and more effectively.
Key features of Collaboration Security for Microsoft Teams
Some of the key features of Collaboration Security for Microsoft Teams include Safe Links, End-user reporting, Zero Auto Purge (ZAP), Simulation and training, and Advanced hunting. Safe Links scans URLs shared in Teams conversations, group chats, or Teams channels for potentially malicious content at the time of click to prevent users from accessing harmful websites.
End-user reporting allows users to report suspicious messages, triggering an alert to the security team. ZAP analyzes messages after delivery and automatically hides those containing malicious content from users.
“Advanced hunting capabilities” allow for querying up to 30 days of raw data and identifying potential threats using custom queries or guided hunting workflows. Simulation and training resources for potential attacks on Teams help users learn how to recognize and report phishing attempts and other malicious activities.
Collaboration Security for Microsoft Teams protects against cyber-attacks that target collaboration platforms like Teams. The feature enhances visibility into the attack landscape by enabling end-user reporting of suspicious messages and providing alerts and insights in the Microsoft 365 Defender portal. To start using Collaboration Security for Microsoft Teams, customers of Microsoft E5, Microsoft E5 Security, or Microsoft Defender for Office 365 can enable the feature by following specific steps outlined in the official announcement:
1. Sign in to Microsoft Security with the linked work or school account.
2. Go to Policies & rules > Threat policies > Safe Links.
3. Under Policies that apply to specific recipients > Global settings > Edit > Settings that apply to content except email > Turn on Safe Links for Microsoft Teams.
4. Under Policies that apply to specific recipients > Global settings > Edit > Settings that apply to content except email > Turn on Track when users click malicious links in supported Office applications.
Tip of the day: To prevent attackers from capturing your password, Secure Sign-in asks the user to perform a physical action that activates the sign-in screen. In some cases, this is a dedicated “Windows Security” button, but the most common case in Windows is the Ctrl+Alt Del hotkey. In our tutorial, we show you how to activate this feature.