A new phishing campaign is targeting Spotify users by tricking them into believing emails are coming from the music streaming service. Attackers are using the cleverest of all phishing lures, making users believe they are interacting with an official company. It's tried, true, and tested, and in this case is harvesting Spotify user credentials.
Research company AppRiver discovered the phishing campaign this month. The whole process relies on creating a convincing email that looks like one Spotify would send.
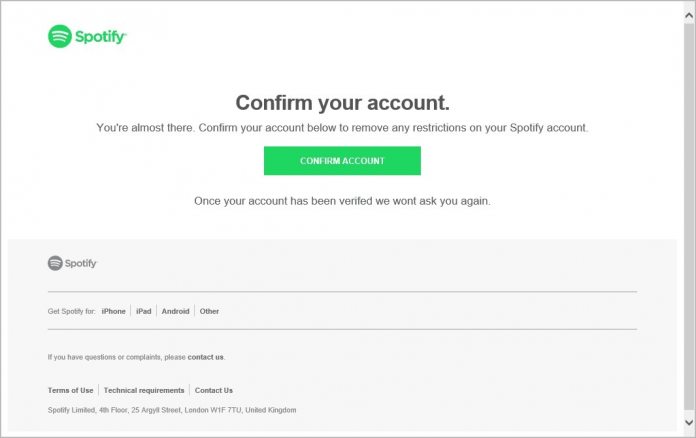
These emails try to fool unwitting users into clicking a link that will lead them to a website that is also designed to deceive by looking like Spotify. Once the user enters the username and password, they will have given the bad actors their credentials.
While there are arguably worse things to have compromised than your Spotify password, Threatpost reports the danger. “Knowing just one password for a victim opens the door to a multitude of attack vectors,” David Pickett, cybersecurity analyst at AppRiver, told Threatpost.
“Knowing how someone creates a password offers a personal glimpse into their password creation mindset and probability of overall attack success,” he said. “This also gives an opportunity for social engineering using the same information which is important to the victim.”
One example password could be Lakers92, which an attacker may deduce means the user likes basketball and was possibly born in 1992.
“That birthday information could be verified by online people data searches (Pipl, Wink, PeekYou, etc.) and lead to finding out all their animal names and important dates in their life,” Pickett added. “Social-media platforms make this reconnaissance extremely simple and valuable.”
Convincing Attack
The Spotify phishing attack is predicated on the ability for the bad actor to trick users. To that end, this attempt is dangerous because both the email and linked landing site a convincing. Of course, for the trained eye, there are some giveaways. For example, in the “from” address bar on the email, the sender is obviously a fake, as is the URL.
It's the same old story, if you check emails carefully then you should be fine.
“The attacker has setup a well-disguised login page that looks identical to the actual Spotify login page,” AppRiver researchers said in a posting this week. “However, they can't hide the actual URL in the web address browser.”