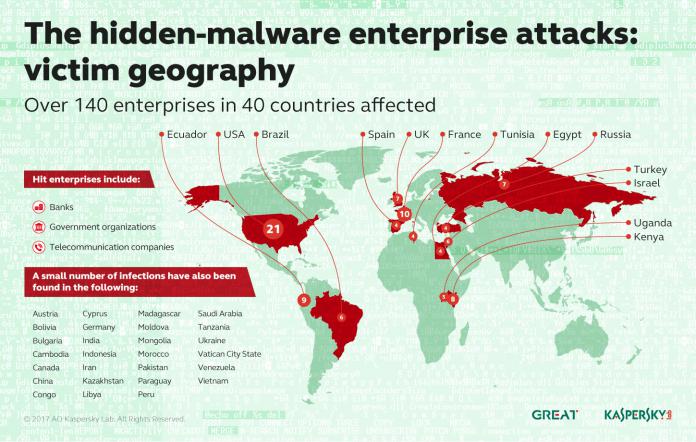
Fileless (or invisible) malware has been known about for over two years. However, it has never been mainstream until now. Kaspersky Labs, the company that first discovered the vulnerability, will publish research on Wednesday to show how over 140 banks and organizations have been affected by the malware.
Moscow-based Kaspersky found the fileless malware two years ago. The company discovered that its corporate network had been breached by a new type of malware. This was a type of hidden vulnerability that resided only in the memory of the infected machine.
Because of this, the malware was able to remain undetected for months. The fileless technique is similar to a previous malware known as Duqu2.0. “Techniques like those described in this report are becoming more common, especially against relevant targets in the banking industry,” Kaspersky explains. “Unfortunately the use of common tools combined with different tricks makes detection very hard.”
The company found that the previously unseen attack was created from Stuxnet, a sophisticated worm that is claimed to have been made by the governments of the United States and Israel. The worm was reportedly built to sabotage Iran’s nuclear program.

Hidden Attacks
While it was discovered two years ago, it has now been mimicked by mainstream hackers. Already the vulnerability has been used to expose more than 140 organizations. Because it is nearly invisible, it is hard for security measures to detect the vulnerability.
Indeed, Kaspersky points out that because the files remain hidden, the number of infected organizations could be much higher. Furthering the danger of the attack, the malware uses legitimate system administrative and security tools, such as PowerShell, as a way to place the malware.
“What’s interesting here is that these attacks are ongoing globally against banks themselves,” Kaspersky Lab expert Kurt Baumgartner told Ars. “The banks have not been adequately prepared in many cases to deal with this.”
Last Updated on February 9, 2017 10:34 pm CET by Luke Jones