Microsoft’s EMET toolkit has been helping to prevent software exploits for over seven years now. According to the Redmond giant, its about time it was put to bed, and an end date of July 2018 has been set.
However, some security experts aren’t too happy with that decision. The computer emergency response team at Carnegie Mellon University is one of those groups. In a blog post titled researcher Will Dormann points out the flaws in Microsoft’s thinking.
Windows 10
According to Microsoft, the EMET Toolkit is superseded by the protections built into Windows 10. A spokesperson for the company says “[EMET’s] effectiveness against modern exploit kits has not been demonstrated, especially in comparison to the many security innovations built-in to Windows 10.”
Dormann doesn’t seem to agree with that statement at all. Microsoft is neglecting a key part of EMET: forcing applications to use secure features. Though Windows 10 offers some better security, it’s defunct if software isn’t compiled to make use of it. Here’s a useful table that points out some of the holes:
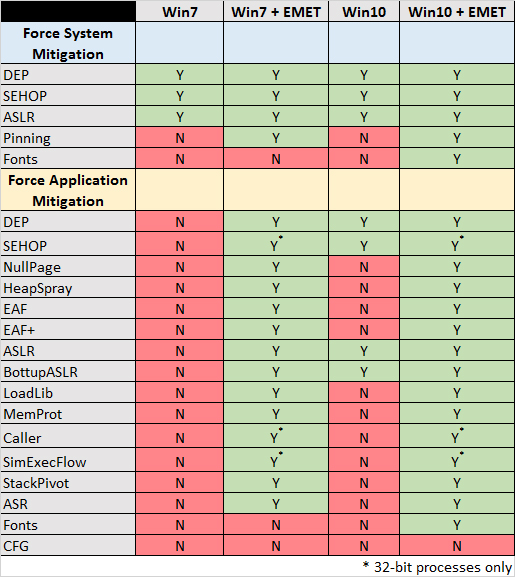
According to Dormann’s research, even a Windows 7 PC with EMET configured would be more secure than Windows 10. This points to a somewhat misleading message from Microsoft, who stated, “Windows 10 includes all of the mitigation features that EMET administrators have come to rely on.”
Though the Redmond giant isn’t planning to cut EMET entirely, there will be no further updates after 2018. This may result in vulnerabilities in some software, and therefore the user.
“It is pretty clear that an application running on a stock Windows 10 system does not have the same protections as one running on a Windows 10 system with EMET properly configured,” says Dormann, who has been working in the industry for over a decade.
It’s difficult to fault his logic, and it will be interesting to hear Microsoft’s response.





