On Wednesday, Microsoft announced Encryption at Rest with Azure Site Recovery (ASR) is now available. The company has moved the service from private preview to Generally Available (GA). Poornima Nataraja, Microsoft Program Manager, Cloud + Enterprise, made the announcement on the Azure blog.
Azure Site Recovery now support Storage Service Encryption (SSE). This helps customers protect data while meeting security and compliance requirements. Microsoft says SSE is a continuance of its commitment to offer enterprise-grade security solutions.
SSE gives Azure Site Recovery users the ability to recreate storage accounts with Encryption turned on. Encryption and be disabled or enabled through Azure Storage Resource Provider REST API. It can also be controlled through the Storage Resource Provider Client Library for .NET, Azure PowerShell, or the Azure CLI.
Protecting Workloads with Encryption
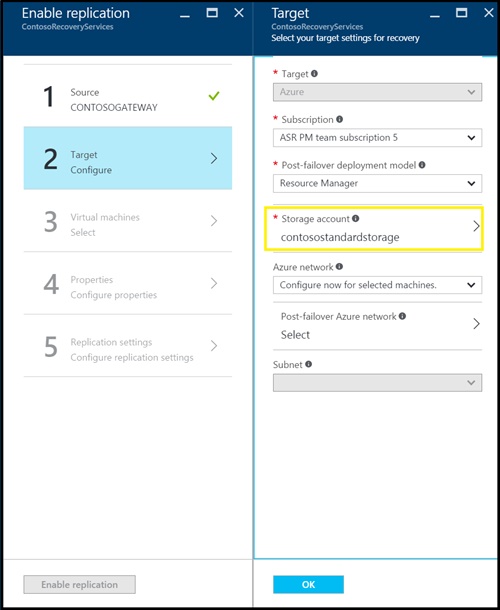
Once encryption has been enabled, customers can specify a storage account they wish to use.
This account will serve as the target location for replicate storage for setting up protection for workloads. Replicated data is then encrypted before storage and decrypted when it is retrieved.
However, Nataraja warns customers that the following things need to be taken into account:
- All encryption keys are stored, encrypted, and managed by Microsoft.
- The experience when using ASR does not change when replicating to SSE-enabled storage accounts.
- If you have been using ASR for protecting your workloads, you can turn on SSE for storage accounts used to store the replicated data. Once you do this, all data replicated to these storage accounts from then on (fresh writes) would be encrypted. Data replicated and stored in these storage accounts prior to enabling SSE would not be encrypted.
- If you intend to replicate your workloads to premium storage, you will need to turn on SSE on both the premium storage account and the standard storage account used for storing replication logs (configured at the time of setting up replication).