Microsoft has announced the release of Azure AD Conditional Access in preview, for iOS, Android, and Windows. The company revealed the launch through the Enterprise Mobility and Security Blog on Wednesday. Conditional Access gives Azure AD corporate users the ability to restrict access to enterprise managed devices.
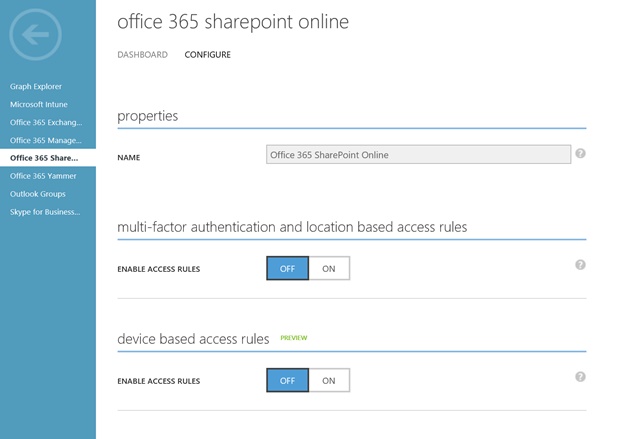
Just last month Microsoft pushed Azure AD Conditional Access per app MFA and Network Location policies to GA. With MFA and Network Location policies, admins can create Conditional Access policies for SharePoint. This is important because it means users will need to be part of the corporate network to access the service.
Azure AD Conditional Access for preview on devices works in a similar manner. It creates policies within the devices that allow businesses to configure access to their needs. The preview is a true cross-platform release. As well as coming to iOS and Android, it is available across Windows 10, Windows 8.1, and Windows 7.
In a blog post to announce the release, Microsoft says policies are set on the following requirements:
“Domain joined devices – You can set a policy to restrict access to devices that are joined to an on-premises Active Directory domain and are also registered with Azure AD. This policy applies to Windows desktops, laptops or enterprise tablets that belong to an on-premises Active Directory domain which have registered with Azure AD. For more information on how to setup automatic registration of domain joined devices with Azure AD, see How to setup automatic Registration of Windows domain joined devices with Azure Active Directory.
Compliant devices – You can set a policy to restrict access to devices that are marked compliant in the directory by the management system. This policy ensures that only devices that meet security policies such as enforcing file encryption on a device are allowed access.”
Azure AD
Conditional Access is functional across any application that authenticates using Azure AD. For example, Azure, Microsoft CRM, and Office 365 can all be managed with the feature. Microsoft also points to a growing number of third-party apps that work with Azure AD CA. These services include SalesForce, Concur, and Service Now.
Organizations can also set up the service for on-premises apps if they have been published through Azure AD.
In June, Microsoft launched three new admin roles for Azure Active Directory. “Privileged Role Administrator”, “Security Administrator” and “Security Reader” were all made available to customers. The same month, the company added enterprise state roaming to sync devices via Azure AD and Windows 10.





