Microsoft has announced that the ability to develop databases using Always Encrypted is now supported in SQL Server Data Tools (SSDT). The company made the announcement on its SQL Server Blog, showing how developers can now create protected data within a database.
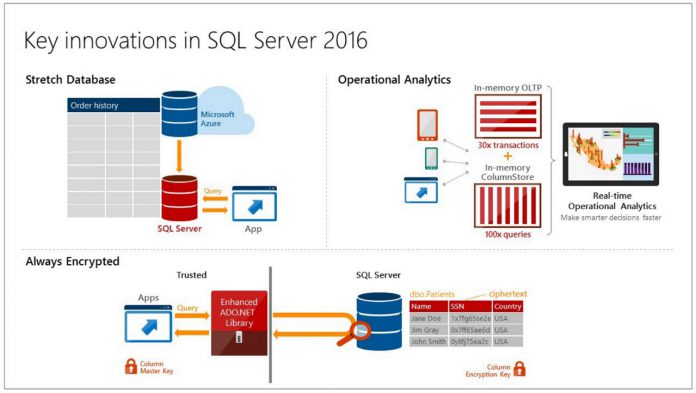
Always Encrypted is available in both SQL Server 2016 and Azure SQL Database and it allows users to protect sensitive data by transparently encrypting and decrypting data sent from the database column.
Microsoft says users will need to have the following installed to access Always Encrypted for SQL Server Data Tools:
- Visual Studio 2013 or Visual Studio 2015.
- SSDT GA July 2016 for Visual Studio 2015 or Visual Studio 2013.
- SQL Server Management Studio (SSMS) GA July 2016. Note: Currently, you need SSMS or the SqlServer PowerShell module that comes with SSMS, to provision Always Encrypted keys. In a future update of SSDT, we will support Always Encrypted key provisioning.
“Always Encrypted is a feature designed to protect sensitive data, such as credit card numbers or national identification numbers (e.g. U.S. social security numbers), stored in Azure SQL Database or SQL Server databases. Always Encrypted allows clients to encrypt sensitive data inside client applications and never reveal the encryption keys to the Database Engine (SQL Database or SQL Server).”
The company says that this feature is rolling out with the July update of SSDT. In its blog, Microsoft explains how to import an existing database into an SSDT project using the Always Encrypted feature.
The process involves importing a Database into a SQL Project, Provisioning a Column Master Key (CMK), Provisioning a Column Encryption Key (CEK), configuring encryption and database columns, building the Project, and then finally verifying the Always Encrypted feature.
At the start of June, Microsoft moved SQL Server 2016 to general availability.