Ransomware continues to be a growing problem and Microsoft is warning users about a new type of attack that can move from one machine to another. The company issued the warning on its Malware Protection Center, which is dedicated to providing information to customers about threats and how to solve them.
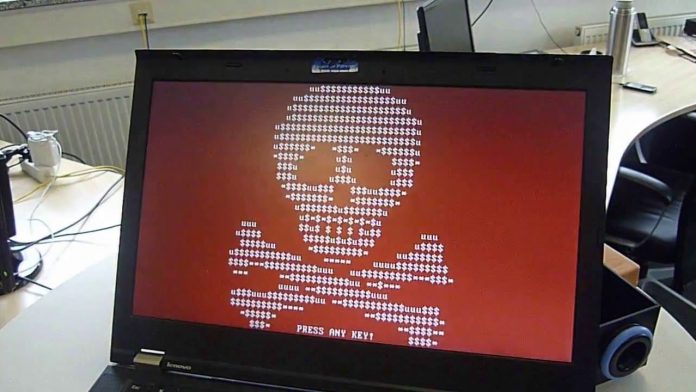
We have covered ransomware often this year as this type of malware continues to grow in popularity. The attack usually shuts down parts or all of a system and literally holds it hostage for a ransom, with the user needing to pay to have the files unlocked. Once paid, it is a lottery whether the files would actually be unlocked.
The new kind of ransomware being reported by Microsoft has the worrying ability to replicate itself once it has infected one PC. This means only one instance of the malware package needs to reach a system for it to potentially spread to other machines through flash and network drives. It would pose a particular threat to companies who have shared networks (i.e. most of them).
Ransomware is always worrying because it can be deployed so easily through a span email or other innocent looking attachment. It would be easy for the new attack, called “Ransom:Win32/ZCryptor.A” or “ZCryptor” to find its way onto one machine before replicating and moving to other computers.
Once executed the malware will run automatically when a system boots, and then drops an autorun.inf in any removable drivers, a “zycrypt.lnk” in the start-up folder, along with a copy of itself as {Drive}:\system.exe and %APPDATA%\zcrypt.exe. This allows the infection to move to other machines, albeit in a hidden file attribute.
Ways of falling victim to ransomware are usually through spam emails which contain an innocent-looking attachment, which in reality is responsible for enabling the malware. However, there seems to be a new way of getting infected. Microsoft, through its Malware Protection Center, is warning its users over a new type of ransomware that actually has the ability to replicate itself and move from one computer to another, through flash drives, as well as network drives.
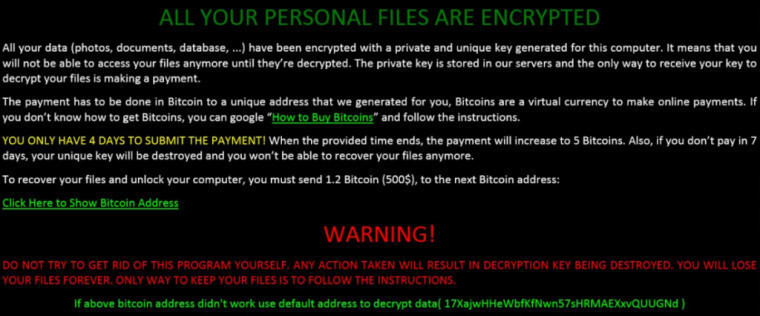
Microsoft reports that once it has encrypted files on a system a HTML file will warn users that their files and systems have been locked. The ransom in this instance is 1.2 bitcoins, or a sizable $500 to pay for the encrypted files to be unlocked. The nefarious program says users must comply within four days or the ransom will be raised to 5 bitcoins.
The Malware Protection Center says infected computers should be restored from a backup, but does add that even this may not work considering other ransomware types have deleted backup files.