A critical account authentication flaw discovered earlier in the week was quickly dealt with by Microsoft, with the company patching the issue within 48 hours.
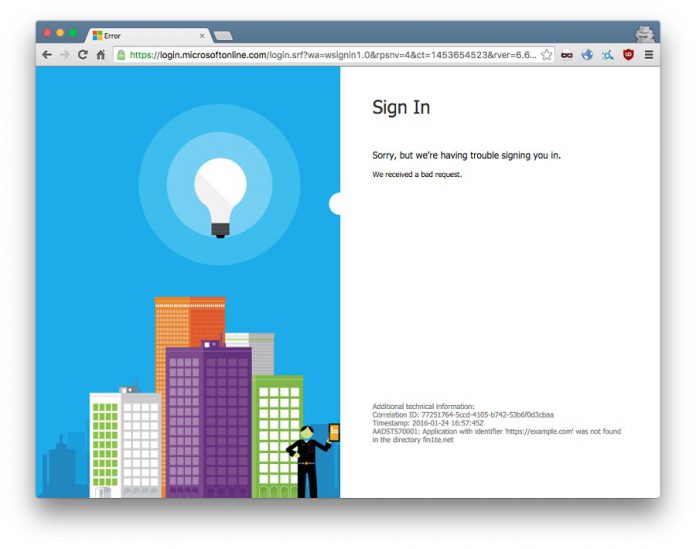
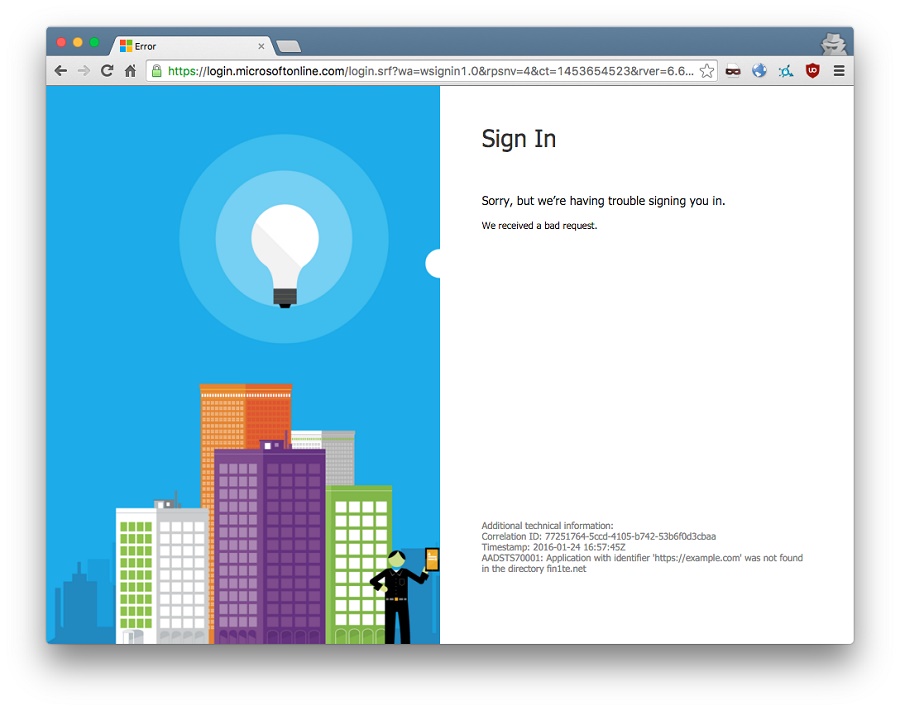
Security expert Jack Whitton said the flaw allows hacker to harvest login tokens through phishing websites to potentially endanger accounts and personal data for users.
Whitton added that attackers could manipulate POST values to allow hackers to impersonate Microsoft products and potentially infiltrate their personal data.
A POST request is sent every time a user inputs their details to enter a service online, with the request coming with a login token.
In the case of Microsoft, this could be for such services as Outlook and Azure, with login tokens for those and other service compromised by the attack. Hackers merely need the tokens to potentially impersonate a user and log in to services. Simply bypassing filters by changing URL coding allowed Whitton to best barriers meant to prevent authentication errors.
“This was quite a fun CSRF to find and exploit,” Whitton said. “Despite CSRF bugs not having the same credibility as other bugs, when discovered in authentication systems their impact can be pretty large.”
The token would only be valid for a single service, but it would be possible to create multiple iframes within URLs to access other services. Whitton reported his findings to Microsoft last Sunday, and the same day Microsoft confirmed the problem and managed to roll out a patch that fixed the issue by Tuesday 26.
It is commendable that Microsoft acted so quickly, taking just 48 hours to fix a problem that most people still did not know existed.
SOURCE: Whitton